This project uses Quarkus, the Supersonic Subatomic Java Framework.
Install first:
- JDK 17
- Maven
- Quarkus CLI
You can run your application in dev mode that enables live coding using:
quarkus devCreate a new Openshift sandbox, then you need to log in from your terminal.
-
Create Kafka instance
- Go to console.redhat.com > Application And Data Services > Streams for Apache Kafka > Kafka Instances > Create Kafka instance
- Name doesn't matter, and you can use default settings
-
Once the cluster has been created, click on it and add Access:
- Go to 'Access' Tab > Manage access
- All Accounts
- Add permissions:
Consumer group is * allow AllTopic is * allow All
- Save
-
Add topics
power,game-eventsanduser-actionswith default config -
In Openshift add "Red Hat OpenShift Streams for Apache Kafka"
-
If you don't have the rhoas cli client yet, get it here: https://access.redhat.com/documentation/en-us/red_hat_openshift_application_services/1/guide/bb30ee92-9e0a-4fd6-a67f-aed8910d7da3#proc-installing-rhoas_installing-rhoas-cli
-
Log in to Red Hat Openshift Application Services:
rhoas login
-
Get an Api token at console.redhat.com/openshift/token
-
Connect your sandbox to the Kafka cluster:
rhoas cluster connect --token YOURTOKEN
-
-
Select instance
-
Deploy Windturbine app
-
Add link in Topology view
-
Start rollout on Windturbine Deployment config
- Create an infinispan cluster in the sandbox console using the "Infinispan Helm chart"
- Name it
infinispan
openssl req -newkey rsa:2048 -new -nodes -x509 -days 3650 -keyout key.pem -out cert.pemoc create secret generic https-secret --from-file=cert.pem=./cert.pem --from-file=key.pem=./key.pemcp src/main/kubernetes/openshift.sandbox.yml src/main/kubernetes/openshift.ymlquarkus build -Dquarkus.kubernetes.deploy=true -Dquarkus.profile=openshift-sandbox -Dquarkus.container-image.group=[project name]quarkus build -Dquarkus.container-image.build=true -Dquarkus.profile=openshift-sandbox -Dquarkus.container-image.group=[project name]oc delete all -l app.kubernetes.io/name=quinoa-wind-turbineTo run this demo you need OpenShift >=4.10 with cluster-admin privileges.
Create an account on Quay.io if you do not already have one.
Create two repositories with public access (pull), you will use credentials in the next step to push container images.
From right-side menu, click Create New Repository
Create a new repository:
- quinoa-wind-turbine
Flag it as Public Repository and click Create Public Repository
- Login to quay.io in the web user interface and click on your username in the top right corner.
- Select account settings.
- Click the blue hyperlink Generate Encrypted Password.
- Re-enter your password when prompted.
- Copy the password
Login to OpenShift Web Console to install prerequisites.
First, create a project for the demo:
oc new-project demo --description='wind-turbine-race'You can choose a different name, but then you have to update argo/wind-turbine-app.yaml before you deploy the app (see below in the Flow section).
OpenShift Pipelines is provided as an add-on on top of OpenShift that can be installed via an operator available in the OpenShift OperatorHub. Follow these instructions in order to install OpenShift Pipelines on OpenShift via the OperatorHub.
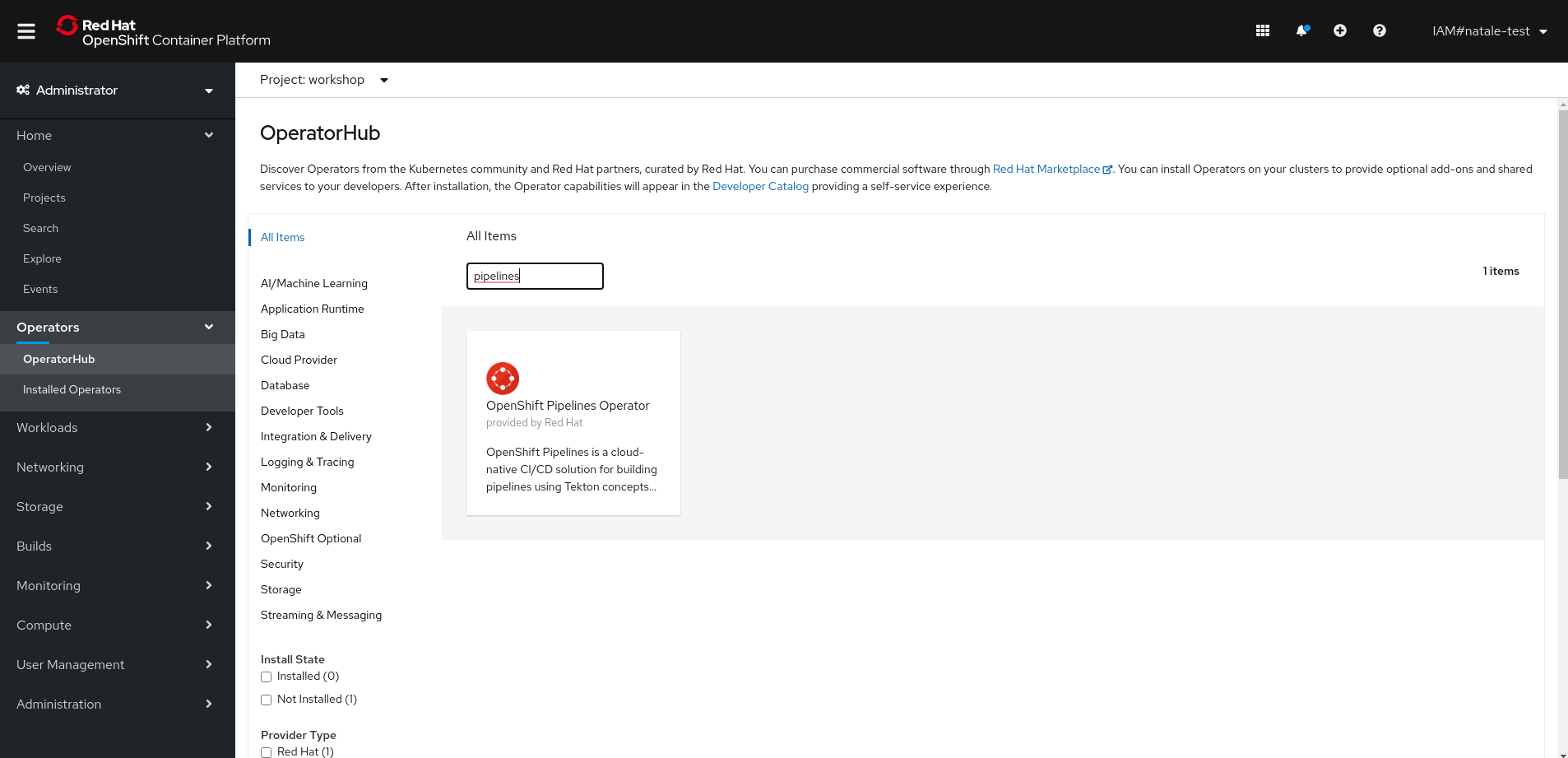
From the left-side menu under Administrator perspective, go to Operators-> OperatorHub. In the search box, search for pipelines, then click to OpenShift Pipelines Operator:
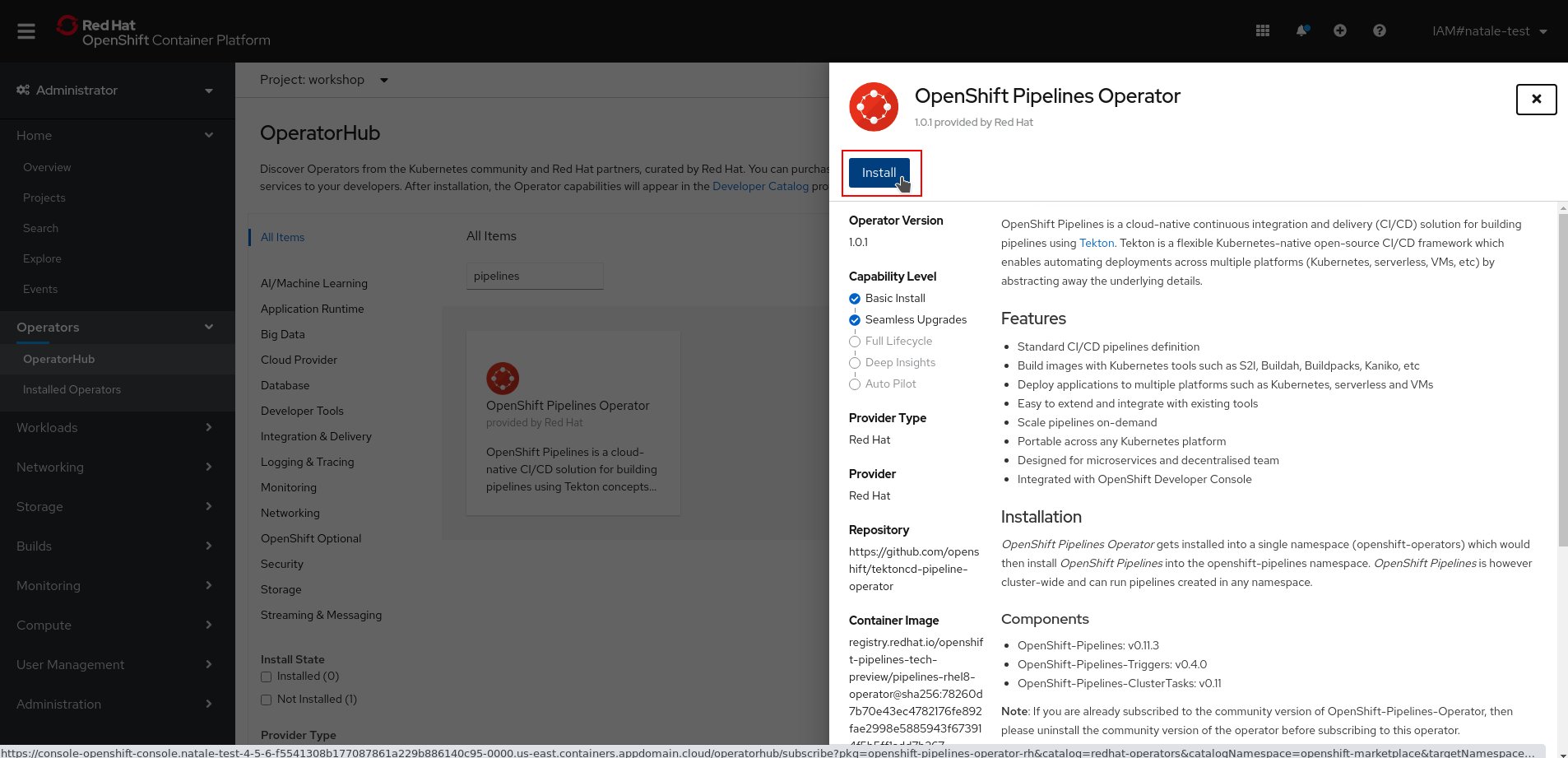
From the description view, click Install to review all installation settings.
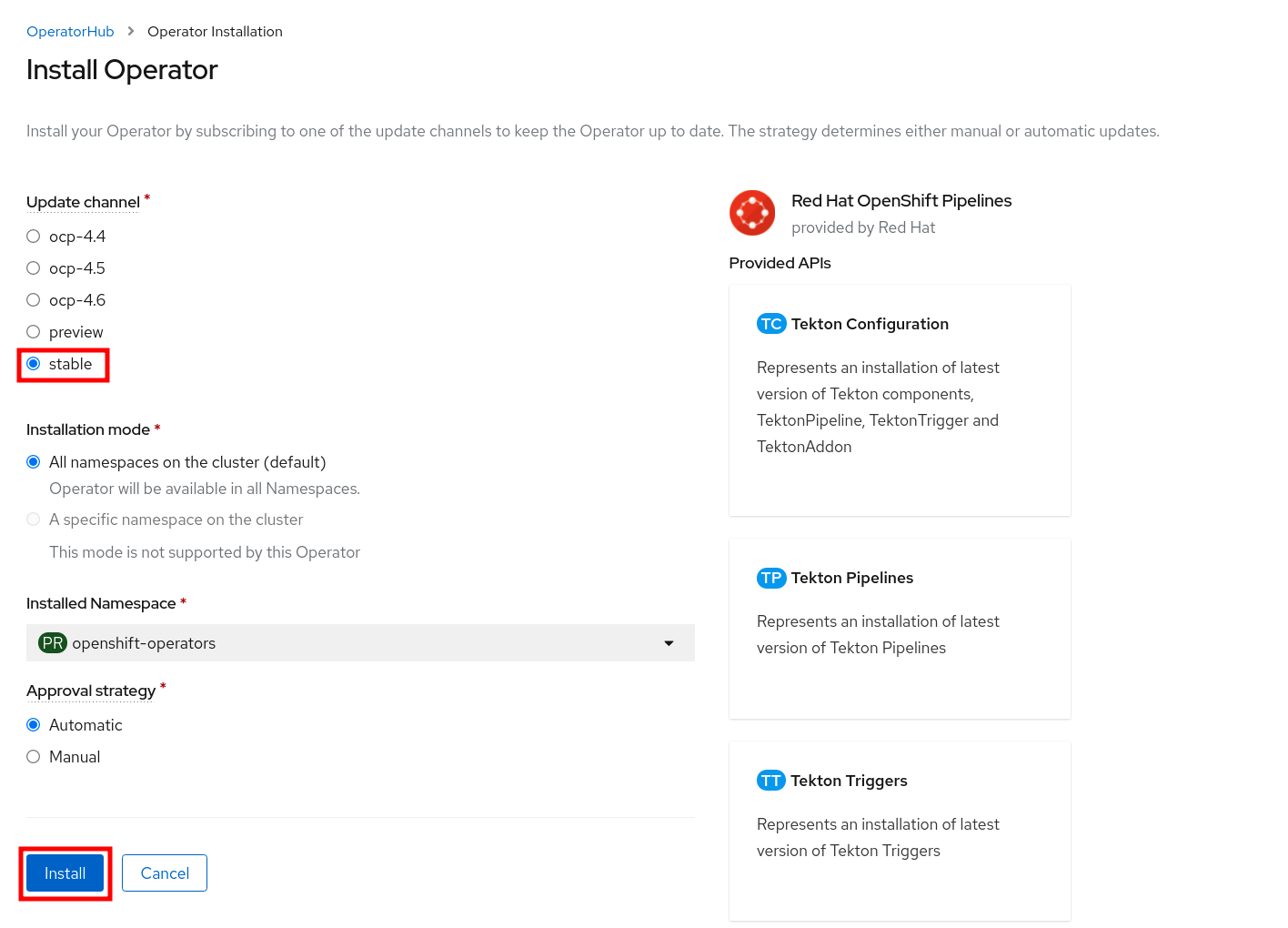
Ensure Update Channel is set to stable , and click Install to start installing the Operator.
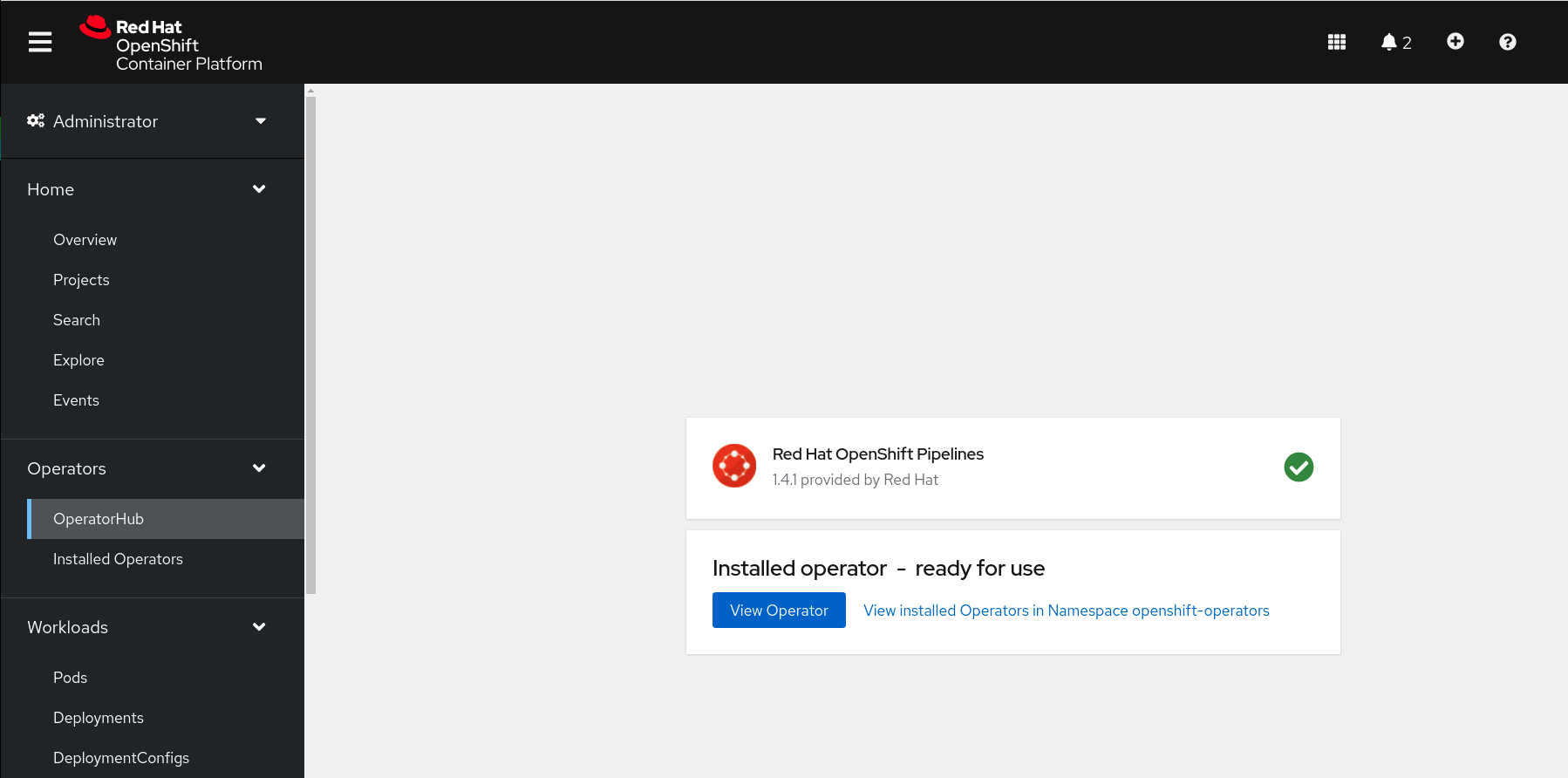
After few seconds, the installation should be completed with success and you can verify it looking at Status column, check if the status is Succeeded.
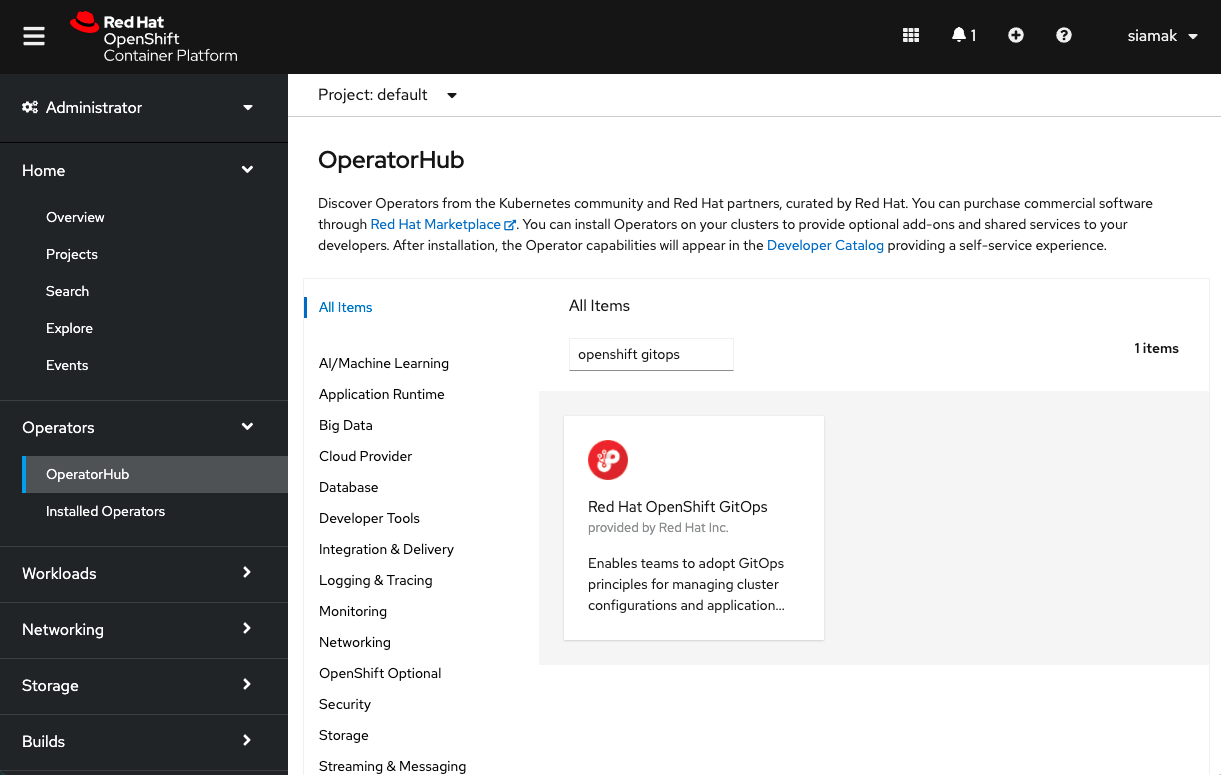
Log into OpenShift Web Console as a cluster admin and navigate to the Administrator perspective and then Operators → OperatorHub.
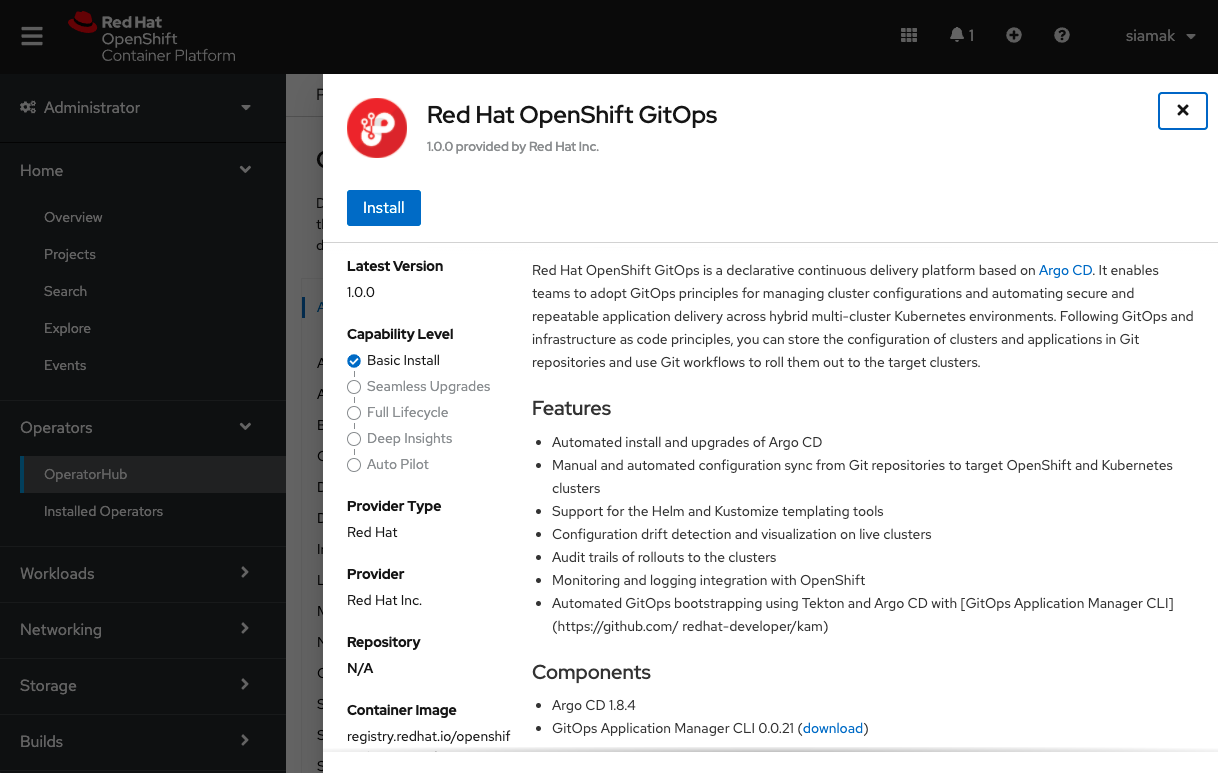
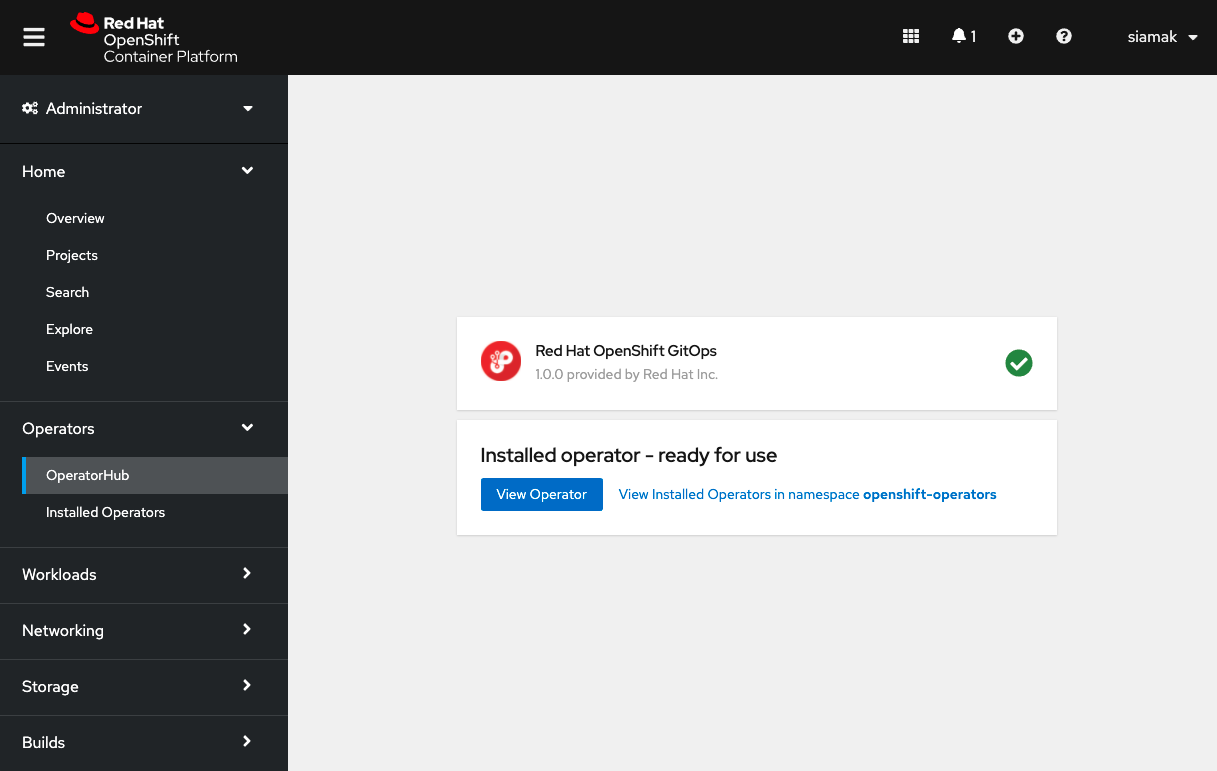
In the OperatorHub, search for OpenShift GitOps and follow the operator install flow to install it.
IMPORTANT Give permission to the Argo CD service account to control the cluster:
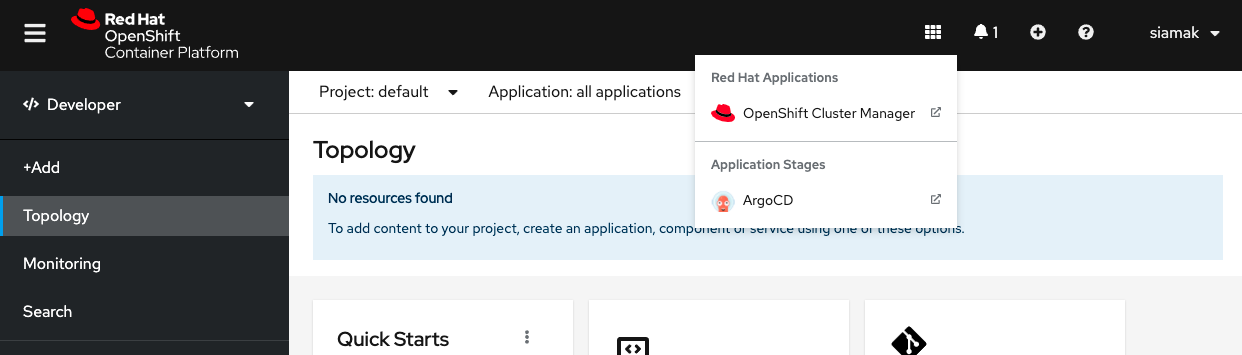
oc adm policy add-cluster-role-to-user cluster-admin -z openshift-gitops-argocd-application-controller -n openshift-gitopsOnce OpenShift GitOps is installed, an instance of Argo CD is automatically installed on the cluster in the openshift-gitops namespace and link to this instance is added to the application launcher in OpenShift Web Console.
Click on Argo CD from the OpenShift Web Console application launcher and then log into your OpenShift credentials using the OpenShift Auth option.
Install AMQ Streams from OperatorHub and create a KafkaCluster named my-cluster
- Create an infinispan cluster from the Web Console using the "Infinispan Helm chart"
- Name it
infinispan
Create a Secret with your Quay.io credentials with the encrypted password you copied before:
oc create secret docker-registry quay-secret --docker-server=quay.io --docker-username=<QUAY_USERNAME> --docker-password=<ENCRYPTED_PASSWORD>Create a Secret with your GitHub Personal Access Token
apiVersion: v1
kind: Secret
metadata:
name: git-user-pass
annotations:
tekton.dev/git-0: https://github.com
type: kubernetes.io/basic-auth
stringData:
username: <github user>
password: <github personal access token>Save it to a file with your credentials and create the secret:
oc create -f git-user-pass.yamlLink Secrets to pipeline Service Account.
NOTE: Pipelines Operator installs by default a pipeline Service Account in all projects. This service account is used to run non-privileged containers and builds across the cluster.
oc secret link pipeline quay-secret
oc secret link pipeline git-user-passFork this repo
In order to enable webhooks, fork this repo
Fork and clone GitOps manifests repo
git clone https://github.com/<yourgithubuser>/quinoa-wind-turbine-manifests
cd quinoa-wind-turbine-manifestsCreate Tekton pipeline manifests
Change the GitOps repo to your fork:
sed -i 's/rhdevelopers/yourquayuser/g' tekton/pipeline-cached.yaml
sed -i 's/redhat-developer-demos/yourgithubuser/g' tekton/pipeline-cached.yamloc apply -f tekton/app-source-pvc.yaml
oc apply -f tekton/build-cache-pvc.yaml
oc apply -f tekton/git-update-deployment.yaml
oc apply -f tekton/maven-task-cached.yaml
oc apply -f tekton/pipeline-cached.yaml
oc apply -f tekton/triggerbinding.yaml
oc apply -f tekton/triggertemplate-cached.yaml
oc apply -f tekton/eventlistener.yaml
oc apply -f tekton/el-route.yaml
Update all references to quay.io with your repos for quinoa-wind-turbine references:
sed -i 's/rhdevelopers/yourquayuser/g' k8s/deployment.yaml
sed -i 's/redhat-developer-demos/yourgithubuser/g' argo/wind-turbine-app.yaml
git add .
git commit -m "update reference to quay and github"
git pushCreate Argo CD Application to deploy the game
oc apply -f argo/wind-turbine-app.yamlStart the Pipeline or edit Config.js to switch to V2:
export const ENABLE_SHAKING = true;Let'encrypt (if the cluster doesn't have a signed certificate):
oc apply -fhttps://raw.githubusercontent.com/tnozicka/openshift-acme/master/deploy/single-namespace/{role,serviceaccount,issuer-letsencrypt-live,deployment}.yaml
oc create rolebinding openshift-acme --role=openshift-acme --serviceaccount="$( oc project -q ):openshift-acme" --dry-run -o yaml | oc apply -f -If the cluster has a signed certificate, create a route with an "edge" tls termination.
- From the operator hub, install Strimzi operator.
- Create a Kafka instance named
my-cluster
- Create an infinispan cluster in the console using the "Infinispan Helm chart"
- Name it
infinispan
cp src/main/kubernetes/openshift.cluster.yml src/main/kubernetes/openshift.ymlquarkus build -Dquarkus.kubernetes.deploy=true -Dquarkus.profile=openshift-cluster -Dquarkus.container-image.group=[project name]quarkus build -Dquarkus.container-image.build=true -Dquarkus.profile=openshift-cluster -Dquarkus.container-image.group=[project name]oc delete all -l app.kubernetes.io/name=quinoa-wind-turbine